Analysis of Computer Network Security Storage System Based on Cloud Computing Environment
DOI:
https://doi.org/10.17762/ijcnis.v14i2.5463Keywords:
Cloud Computing, Network Security, Encryption method, Cloud storage system, IaaS, Data encryptionAbstract
A fundamental component of cloud computers from a business perspective is that users are allowed to use any desire and pay with a product that desire. Its cloud services were accessible anytime and anywhere consumers needed them. As a result, consumers are free to purchase whatever IT services they want, and they don't have to worry about how easy things can be managed. The remote server is used in a new information storage computing architecture that is considered an Internet generation. Ensuring security, material at resource providers' sites is a challenge that must be addressed in cloud technology. Thus, rather than reliance on a single provider for knowledge storing, this research implies developing construction for protection of knowledge stockpiling with a variation of operations, in which knowledge is scrambled and divided into numerous cipher frames and distributed across a large number of provider places. This support was applied to provide greater security, scalability, or reliability that was suggested according to the new structure. This paper, presented an encoded model for the cloud environment to improve security. The proposed model comprises the parity metadata for the database management provision to the provider. In the developed encoder chunks parity is not stored within the single resources with the provision of the available information chunks. The constructed security architecture in the RAID layer increases the dependability of the data with the deployment of the RAID 10 deployment. The developed RAID-based encoder chunks exhibit improved efficiency for the higher uptime at a minimal cost.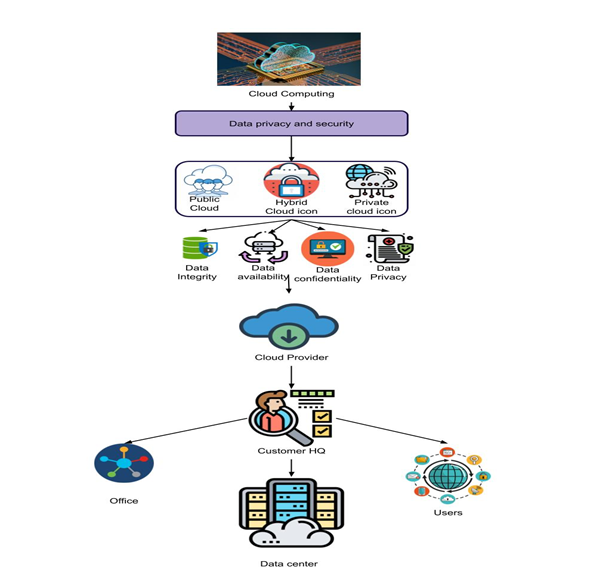
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2022 Author

This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License.